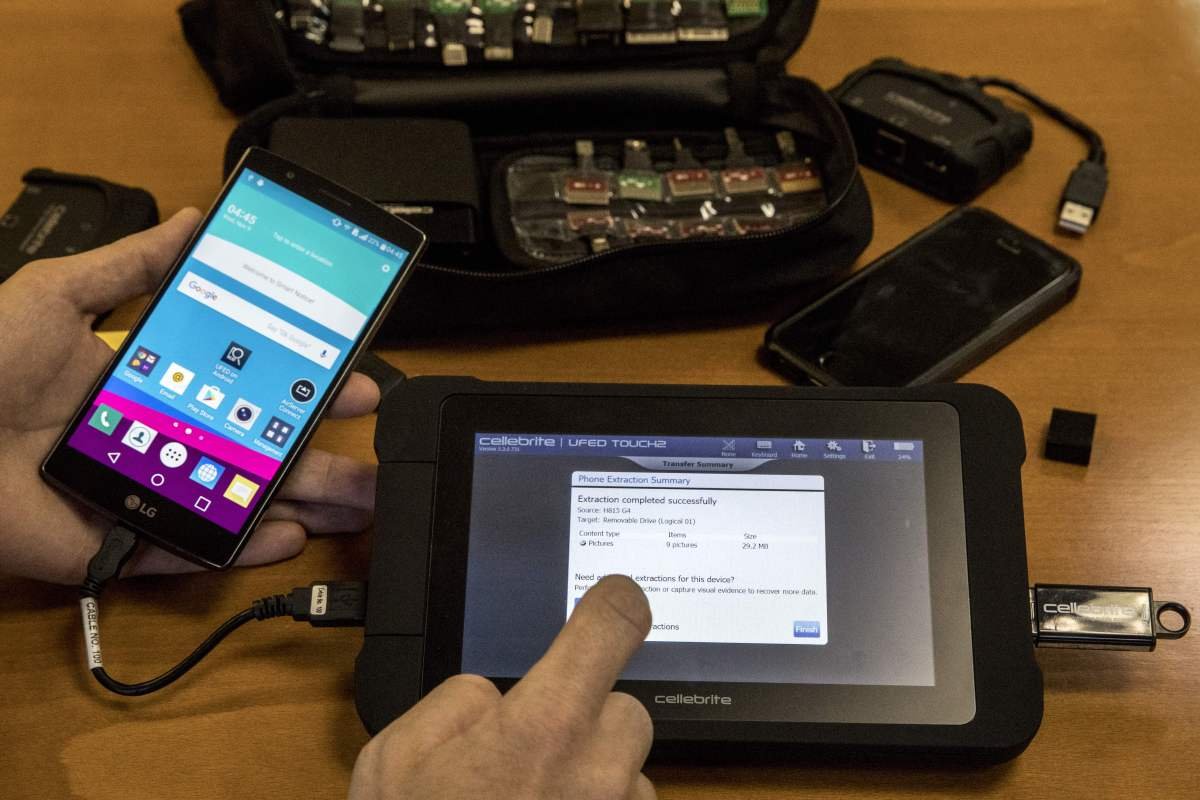
Last year, phone-hacking tool maker Cellebrite announced it had suspended Serbian police as a customer after human rights researchers alleged local police and intelligence agencies used its tools to hack into the phones of journalists and activists and spread spyware.
This was a rare instance of Cellebrite publicly cutting off a customer after documented allegations of abuse, citing an Amnesty International technical report.
However, following recent similar allegations of abuse in Jordan and Kenya, the Israel-based company responded by denying the allegations and refusing to commit to an investigation. It’s unclear why Cellebrite changed its approach, which appears to contradict its previous actions.
On Tuesday, researchers from The University of Toronto’s The Citizen Lab published a report claiming that the Kenyan government used Cellebrite tools to unlock the phone of local activist and politician Boniface Mwangi while he was in police custody. In another report from January, The Citizen Lab accused the Jordanian government of using Cellebrite tools to hack into the phones of several local activists and protesters.
In both investigations, Citizen Lab, an organization that has investigated the misuse of spyware and hacking technology around the world, based its conclusions on finding traces of a specific application associated with Cellebrite on the victims’ phones.
The researchers said the traces are a “highly credible” signal that someone used Cellebrite’s unlocking tools on the phones in question, as the same app was previously found on VirusTotal, a malware repository, and was signed with digital certificates owned by Cellebrite.
Other researchers have also linked the same app to Cellebrite.
“We do not respond to speculation and encourage any organization with specific, evidence-based concerns to share them directly with us so we can respond,” Victor Cooper, a Cellebrite spokesperson, told TechCrunch in an email.
When asked why Cellebrite acted differently than in the case of Serbia, Cooper said that “the two situations are incomparable” and that “high confidence is not direct evidence”.
Cooper did not respond to several follow-up emails asking if Cellebrite would investigate The Citizen Lab’s latest report and what, if any, differences there are with its case in Serbia.
Contact us
Do you have more information about Cellebrite or other similar companies? From a non-working device, Lorenzo Franceschi-Bicchierai can be reached securely on Signal at +1 917 257 1382 or via Telegram, Keybase and Wire @lorenzofb or email.
As part of its investigations in both Kenya and Jordan, The Citizen Lab reached out to Cellebrite before the reports were released to give the company a right of reply.
In response to Jordan’s report, Cellebrite said “any justified use of our tools in violation of human rights or local laws will result in immediate disability,” but did not commit to investigating the case and declined to share specific customer information.
As for the Kenyan report, Cellebrite acknowledged receipt of The Citizen Lab’s inquiry but did not comment, according to John Scott-Railton, one of The Citizen Lab’s researchers who worked on the Cellebrite investigation.
“We are calling on Cellebrite to disclose the specific criteria they used to approve the sale to the Kenyan authorities and disclose how many licenses have been revoked in the past,” Scott-Railton told TechCrunch. “If Cellebrite is serious about their rigorous vetting, they should have no problem publishing this.”
Following previous reports of abuse, Cellebrite, which claims to have more than 7,000 law enforcement customers worldwide, cut ties with Bangladesh and Myanmar as well as Russia and Belarus during 2021. Cellebrite previously said it had stopped selling to Hong Kong and China following a US government order restricting the export of sensitive technology to the country. Local activists in Hong Kong have accused authorities of using Cellebrite to unlock protesters’ phones.