Lockdown mode on iPhone is for users who face serious threats to their digital security
Apple’s Lock Mode is just one of many ways to keep your iPhone data safe, the FBI has found out again.
In January 2026, the FBI raided the house The Washington Post journalist Hannah Natanson and removed the devices, including the iPhone. Natanson and her paper immediately filed a court motion that currently means the FBI is barred from searching the devices — but she tried.
The FBI is investigating alleged leaks of classified information to the press. There are constitutional issues about whether the FBI can raid a person’s home and apparently have the legal right to force Natanson to unlock his MacBook Pro with Touch ID.
“This extraordinary, aggressive action is deeply troubling and raises deep questions and concerns about the constitutional protections of our work,” The Washington Post Executive Editor Matt Murray told staff.
However, court documents show that during the time the FBI was trying to search Natanson’s devices, it was unable to access her iPhone. As you noticed 404 mediaThe FBI’s filing opposing the return of Natanson’s devices says that:
Because the iPhone was in locked mode, CART (Computer Analysis Response Team) could not extract this device. Similarly, it has not yet been possible to photograph a personal MacBook Pro.
Lock mode
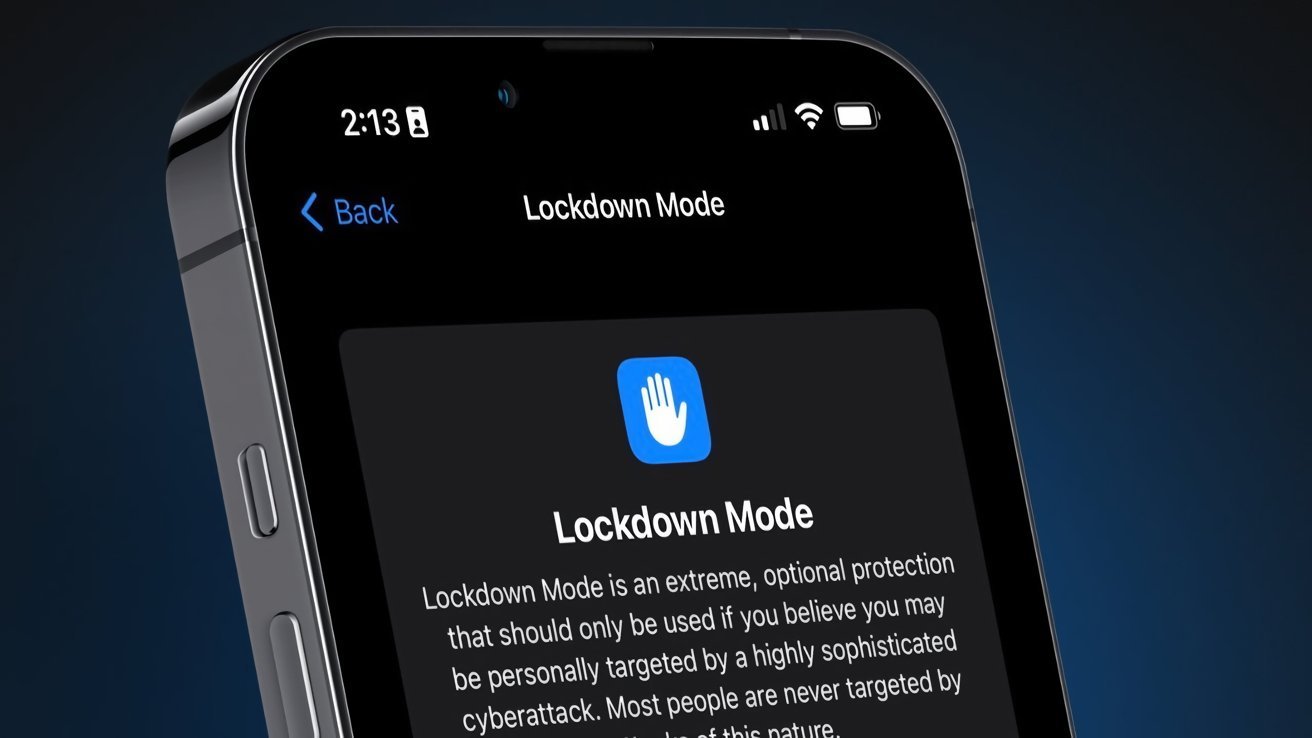
Lockdown Mode, which was introduced in 2022, is an optional feature that Apple said is for people facing “serious, targeted threats to their digital security.” When enabled, lock mode:
- Blocks most types of message attachments
- Disables technologies such as just-in-time JavaScript compilation
- Stops wired data connections
- Prevents installation of new configuration profiles
Lock mode is an optional feature that must be set.
At launch, Apple offered a $2 million reward to any security researchers who could crack it. Apple also said it will continue to add new protections.
In this particular case, it is not clear what happened at Natanson’s home. While the FBI says it was unable to view (or copy) her MacBook Pro, earlier reports say officers forced her to unlock it.
While Natanson allegedly told the agents she wasn’t using biometric authentication, they let her use her finger on the Touch ID button and it unlocked.
With the iPhone, it would appear that Natanson does not use biometrics. Allegedly, the three warrants the FBI had included the right to force her to unlock using Face ID.
According to court documents, Natanson was told at her home that “although she was not required to provide her passcodes, the FBI could use her biometrics to open any devices.”
It’s not at all clear why the warrants with this exceptional permission didn’t also mean she was required to give the agents her PIN.
What Apple Protects
Lock Mode is available to all iPhone owners, although it is not recommended for regular users. Apple calls it “extreme protection” against cyberattacks, and using it means giving up some of the usual benefits of the iPhone.
In addition to features that seem security-related, such as blocking attachments in Messages, Lock Mode also disables shared photo albums. Game Center is also disabled and “Focus and any related status will not work as expected.”
However, Lockdown Mode isn’t Apple’s only method of protecting user security. It has what it calls a “restart from idle” that is automatically in place for all users.
Starting with iOS 18.1 in 2024, if the user does not unlock their iPhone after some unknown period of time, the device will restart itself. Law enforcement officers are not fans.
The idea is that this protects the user because it means the iPhone restarts in a “before first unlock” (BFU) state. In this state, the iPhone is more secure than after the user has unlocked it.

Advanced Data Protection encrypts most of an iPhone user’s data
All iPhones – with the exception of the UK – now also have advanced data protection. This is for all users, regardless of whether they are directly at risk or not, as it ensures everything from device backups to wallet passes through encryption.
What Apple will provide law enforcement
Apple maintains a 21-page, 10,000-word “Legal Process Guidance” document that details what it will and can do when it receives a subpoena. Apple’s document and procedures are updated, but it generally states that Apple:
- Details of the user’s iCloud account
- Access any unencrypted data stored there
That’s about it, and especially since most user data is encrypted, there’s ultimately little that even Apple can gain.
Also note that this information is not given randomly. Requests for details must be accompanied by a subpoena or even a court order. But in cases like the San Bernardino shooting, Apple provided that detail.
Alternatives to Apple
In 2020, the FBI pressed Apple to unlock certain iPhones, but was also able to crack the encryption on the then-new iPhone 11 Pro Max on its own. The agency reportedly used the third-party forensics tool GrayKey.
Security and user privacy are constantly at odds with each other, and each side is constantly updating its technology. In November 2024, it was announced that GrayKey was blocked from all data by iOS 18.1.
Even when this news became public, it was likely that GrayKey had moved on. Now, some 14 months later, it is not known whether the forensics tool is still effectively blocked.
It would appear so, as the FBI was unable to unlock Natanson’s iPhone. However, there is no confirmation that these agents had the tool.
It is confirmed that the agency is unwilling to back down from seizing Natanson’s facilities.
“Ms. Natanson and her employer, the Washington Post, claim that the government’s seizure of this evidence violated the First Amendment and that it must be returned to them,” the FBI court filing said. “He’s wrong.”