Exclusively brought to you by 9to5Mac Security Bite Mosyle, Apple’s only unified platform. Everything we do is to keep Apple devices working and safe for businesses. Our unique integrated approach to management and security combines state-of-the-art Apple-specific security solutions for fully automated Hardening & Compliance, Next Generation EDR, AI-powered Zero Trust and exclusive Privilege Management with the most powerful and advanced Apple MDM on the market. The result is the fully automated Apple Unified Platform, now trusted by more than 45,000 organizations, enabling millions of Apple devices to work effortlessly and affordably. Ask for EXTENDED PRACTICE TESTS today and you’ll understand why Mosyle is everything you need to work with Apple.
Earlier this week, Apple surprised users with the first beta version of iOS 26.4 for iPhone. Many were disappointed (myself included) when the update did not include the much-anticipated improvements to the strange assistant Siri. However, this was nowhere near a featureless update. iOS 26.4 beta 1 introduced at least forty new features and changes, including notable upgrades to RCS and device theft protection.

E2EE for RCS messaging (beta)

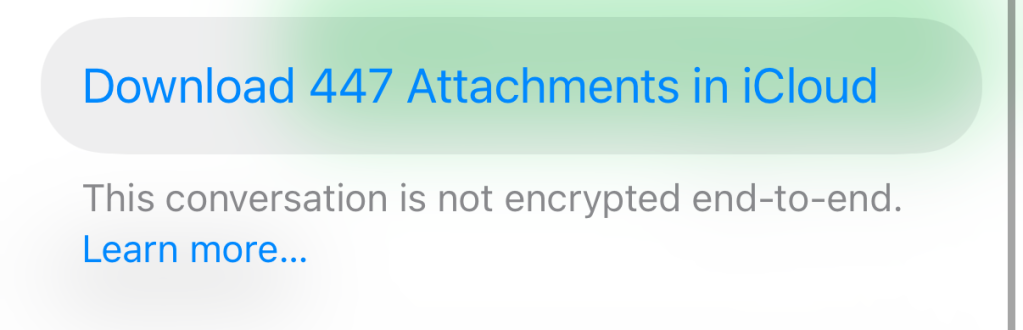
In March 2025, the equivalent of a decade of technology years, Apple announced that it was leading a cross-industry effort to bring end-to-end encryption (E2EE) to the RCS Universal Profile. I previously predicted that it would be revealed at WWDC25. That didn’t happen. In fact, it’s been almost a year of radio silence from Apple until this week, when the company dropped the first iOS 26.4 beta and finally offered the first signs of life for a feature I was beginning to think was DOA.
Apple added RCS support for iPhone in iOS 18 beta 2 to improve the messaging experience with Android users. It was a welcome move for people with parents who refused to get an iPhone (Hi, Dad).
Unlike the now old SMS industry standard, RCS offers familiar features such as read receipts, classic typing indicator animation, audio messages, and improved image size and quality, but also adds the option for better privacy and security.
The key word here is “ability”.
There is a common misconception that RCS comes with E2EE baked in, but this is not the case. Basically, Google’s Messages app is to blame. It was one of the most used RCS clients, offering E2EE between Android devices as an additional layer of security for service users. This is similar to how iMessage provides E2EE exclusively between Apple devices.
When an iPhone communicates with a non-Apple device via RCS, messages are encrypted only in transit using transport layer encryption (such as TLS). While this protects against basic interception in transit, it does not guarantee that messages cannot still be accessed on the server side, unlike E2EE where only the sender and recipient can read the content.
An option to test the feature is now available in iOS 26.4 beta 1. However, Apple states that not all carriers and devices support RCS encrypted messages. You can tell if it has been established by the message thread marked “Encrypted”. I haven’t had much luck switching existing threads to E2EE. This feature seems to only apply to newly created ones now.
Stolen device protection is now on by default
iPhone theft is still common, especially in some parts of Europe. Stolen Device Protection is Apple’s solution for protecting data stored on your iPhone. It is now on by default!
The function was created after The Wall Street Journal Joanna Stern published an investigative report on the rise of iPhone thieves around restaurants and bars.
The attacks were typically carried out by watching victims enter their passcode before stealing the device, changing their Apple ID password and turning off Find My iPhone to prevent remote tracking or erasure. From there, the thief can lock victims out of their accounts (i.e. Venmo, CashApp, other banking apps, etc.) using passwords stored in the Keychain password manager.
Stolen Device Protection completely thwarts this vulnerability in two key ways. This feature requires Face ID or Touch ID authentication (without a backup password) before users can change important security settings, such as Apple ID passwords or device passcodes.
It also allows for a one-hour security delay before users can change important security settings. Designed to give victims time to mark the iPhone as lost (and wipe it) before the thief can make changes. This can be set to “Always” or “Away from known places”.

Let me know in the comments if you have a favorite iOS or Mac security feature.
Fsay Arin: Twitter/XLinkedIn, threads
Subscribe to the 9to5Mac Security Bite Podcast for bi-weekly in-depth coverage of the latest headlines and interviews with Apple’s top security experts:


FTC: We use automatic affiliate links with income. More.